[ad_1]
The source code for the BlackLotus UEFI bootkit has been leaked online, providing insight into a malware that has raised serious concerns among businesses, governments and the cybersecurity community.
BlackLotus is a UEFI bootkit targeting Windows that bypasses Secure Boot on fully patched Windows 11 installationsevades security software, persists on an infected system, and executes payloads with the highest privilege level of the operating system.
Its features include tampering with BitLocker data protection feature, Microsoft Defender Antivirus, and Hypervisor Protected Code Integrity (HVCI) – also known as Memory Integrity feature which protects against attempts to exploit the Windows kernel.
Windows Secure Boot is a security feature that blocks untrusted boot loaders on computers with Unified Extensible Firmware Interface (UEFI) firmware and a Trusted Platform Module (TPM) chip. This security feature is intended to prevent rootkits from being loaded during the boot process and to evade detection by applications running on Windows.
BlackLotus was the first discovered example of a UEFI boot kit capable of bypassing the secure boot mechanism and disabling operating system-level security protections. This was accomplished initially by exploiting the “Baton Drop” vulnerability (CVE-2022-21894), which Microsoft fixed in January 2022.
Workarounds were found for the security update, allowing BlackLotus to continue working and forcing Microsoft to catch up by revoking additional Windows boot managers.
This led to another security update for CVE-2023-24932 (another Secure Boot security feature bypass) that revoked other malicious boot managers.
However, Microsoft disabled security update for CVE-2023-24932 by defaultforcing Windows users to perform a lengthy and somewhat complicated manual installation to fix their systems.
As Microsoft warned that improper installation of the security patch could leave your system unbootable or recoverable from Windows installation media, many opted out of installing the update, leaving devices vulnerable to attacks from secure boot bypass.
“If you are using Secure Boot and do not complete the steps in this article correctly, you may not be able to boot or recover your device from media,” Microsoft explained in a support bulletin.
“This may prevent you from using recovery media, such as external discs or drives, or network boot recovery, if the media has not been properly updated.”
Due to the concern and stealthiness of the BlackLotus malware, both Microsoft and the Guidance shared by the NSA on Windows bootkit detection and removal.
The leaked BlackLotus source code
BlackLotus was originally sold on hacker forums for as little as $5,000, allowing threat actors of all skill sets access to malware typically associated with state-sponsored hacking groups.
However, the threat actor kept the source code private, offering rebuilds for $200 to customers who wanted to customize the bootkit.
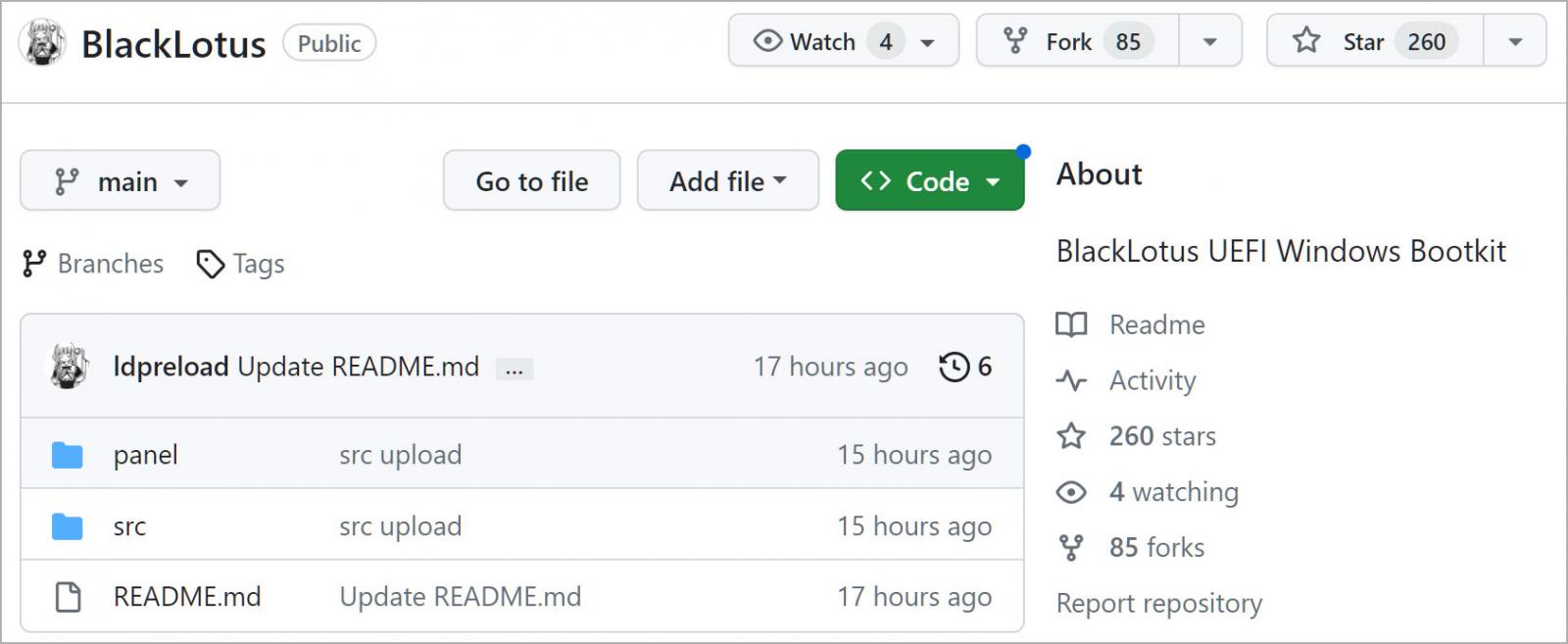
Today, security firm Binarly told BleepingComputer that the source code for the BlackLotus UEFI bootkit is leaked on GitHub by user ‘Yukari.’ making the tool widely accessible to all.
Yukari says the source code has been modified to remove the Baton Drop vulnerability and instead uses the rootkit UEFI bootlickerwhich is based on CosmicStrand, moon bounceAnd SPECTRUM UEFI APT rootkits.
Source: BleepingComputer
“The leaked source code is not complete and mainly contains the rootkit part and the bootkit code to bypass Secure Boot,” said Binarly co-founder and CEO Alex Matrosov.
Matrosov says the bootkit techniques are no longer new, but the source code leak makes it trivial for threat actors to combine the bootkit with new bootloader vulnerabilities, known or unknown.
“Most of these tricks and techniques have been known for years and have no significant impact,” Matrosov told BleepingComputer during a chat about the leak.
“However, the fact that it is possible to combine them with new exploits like the BlackLotus campaign did was something unexpected for the industry and shows the true limitations of current mitigations under the operating system. “
It is important to point out that although Microsoft has fixed the Secure Boot bypasses in CVE-2022-21894 and CVE-2023-24932, the security update is optional and the fixes are disabled by default.
To secure systems against the BlackLotus UEFI Boot Kit threat, be sure to follow the comprehensive mitigation guidance the NSA released last month.
With the source code for the bootkit now widely available, it is also possible that skilled malware authors will create more powerful variants capable of circumventing existing and future countermeasures.
Matrosov told BleepingComputer that this particular attack vector has significant advantages for attackers and will only become more sophisticated and complex.
[ad_2]
Source link
