[ad_1]
The developers of the BlackLotus UEFI Boot Kit have enhanced the malware with secure boot bypass capabilities that allow it to infect even fully patched Windows 11 systems.
BlackLotus is the first public example of UEFI malware capable of bypassing the secure boot mechanism, thus allowing the security protections provided with the operating system to be disabled.
The malware could be used to tamper with BitLocker data protection feature, Microsoft Defender Antivirus and Hypervisor Protected Code Integrity (HVCI) – also known as Memory Integrity feature which protects against attempts to exploit the Windows kernel.
UEFI (Unified Extensible Firmware Interface) is the software that connects the operating system to the hardware that runs it.
This is low-level code that runs when the computer boots and dictates the boot sequence before the operating system starts any of its routines.
BlackLotus Commodities Bootkit
BlackLotus UEFI Malware appeared last year promoted on hacking forums with a feature set that makes it virtually invisible to antivirus agents installed on the compromised host.
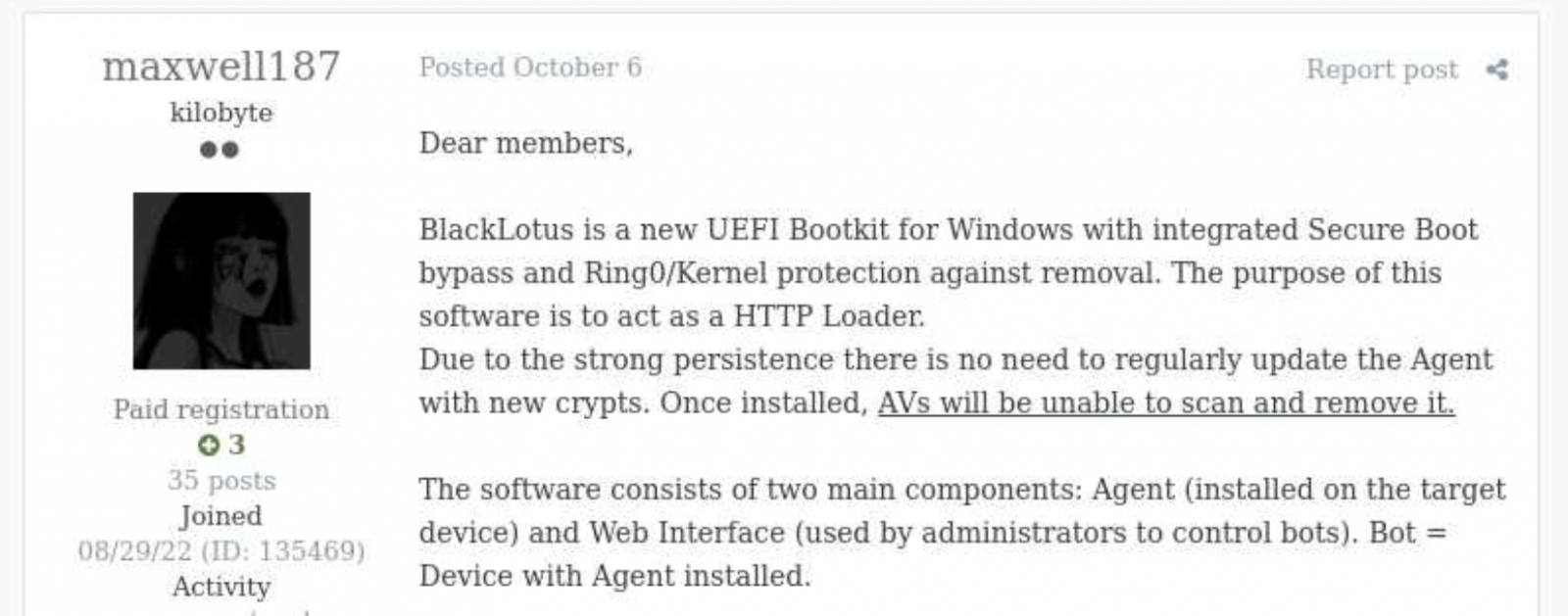
source: KELA
The advertiser said the malware only takes up 80KB after installation and the cost to license is $5,000, although rebuilds are available for just $200.
In a report published this week, ESET security researchers confirmed that the malware works exactly as advertised and can bypass the Secure Boot mechanism by exploiting a vulnerability from last year identified as CVE-2022-21894.
More information on why security updates for CVE-2022-21894 are not blocking this malware is available below.
Their investigation started from an HTTP downloader which turned out to be the user-mode component of the BlackLotus UEFI starter kit, which communicates with the command and control (C2) server and can load other payloads (user/kernel mode).
BlackLotus infection chain
ESET Malware Finder Martin Smolar note that the attack begins by running an installer that deploys the bootkit files to the EFI system partition, disables HVCI and BitLocker protections, and reboots the host.
The attacker relies on legitimate binaries vulnerable to CVE-2022-21894 (Windows Hypervisor Loader, Windows Boot Manager, PE binaries) and their custom Boot Configuration Data (BCD).
Persistence on machines with UEFI Secure Boot enabled is achieved after initial reboot by exploiting CVE-2022-21894 and registering the attacker’s Machine Owner Key (MOK).
The self-signed UEFI boot kit is launched after another reboot and the malicious kernel driver and HTTP downloader are deployed to complete the malware installation.
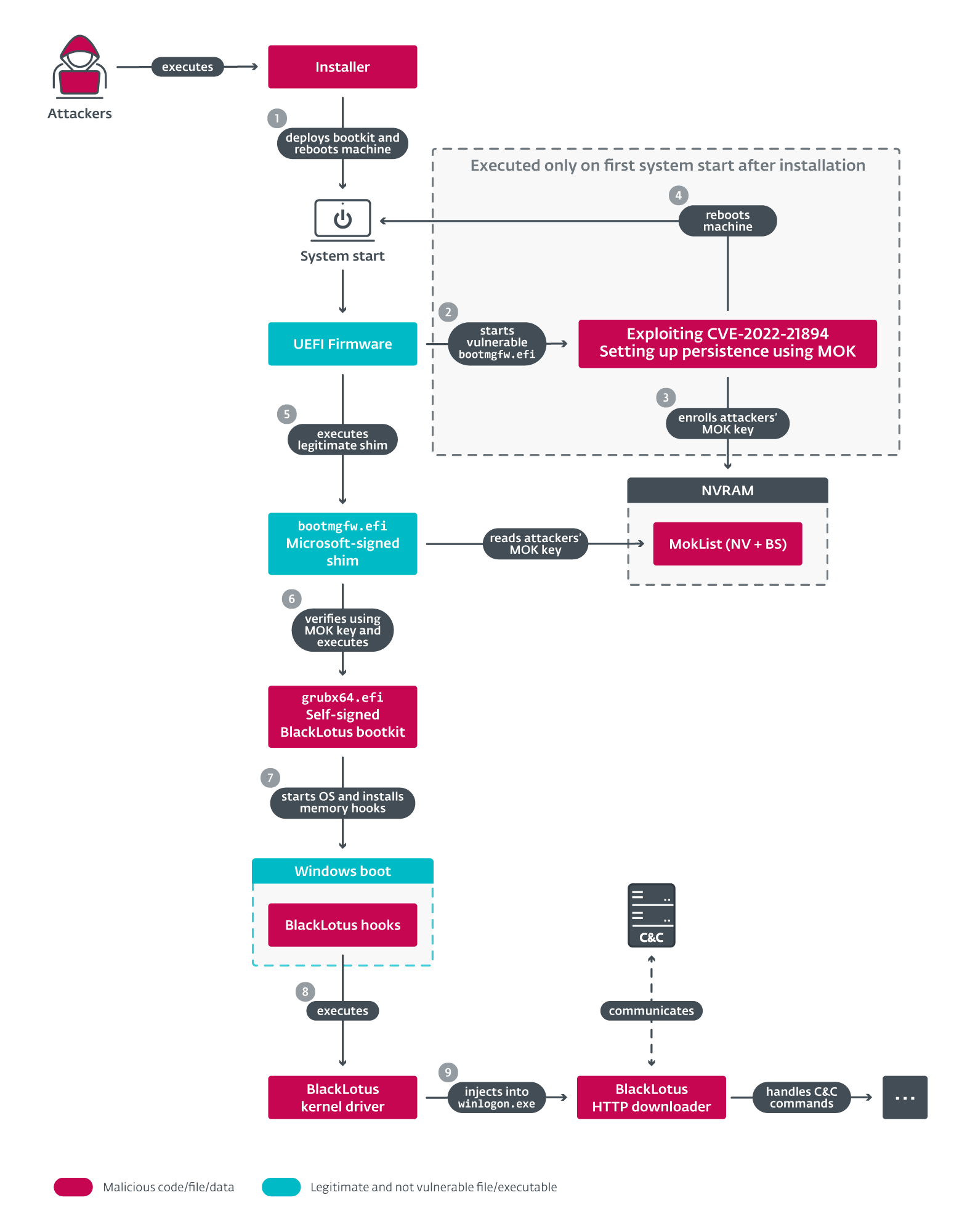
source: ESET
Among the artifacts discovered in the BlackLotus code are references to the Higurashi anime series When They Cry, including the names of two components and the issuer of the self-signed certificate for the bootkit binary.
Another reference that the author of BlackLotus left in the malware code is for unused strings that decipher into messages for the Polish malware analyst. Alexandre Doniec.
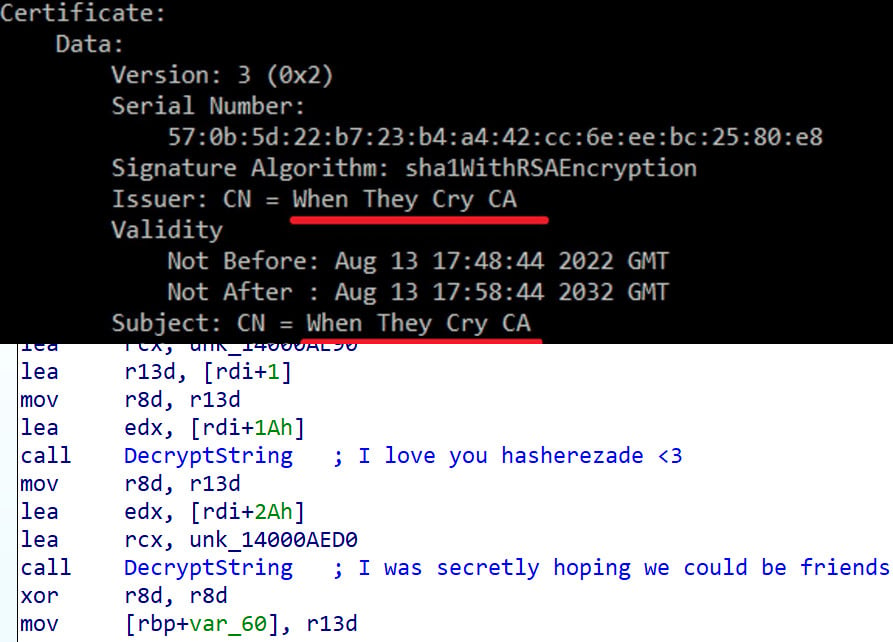
source: ESET
Bug fixed, security risk persists
ESET says the BlackLotus installer can be online or offline, the difference between them is that the offline variants carry the vulnerable Windows binaries.
The online version of the installer downloads Windows binaries “directly from the Microsoft Symbol Store”.
Researchers have seen the three files below being abused by the bootkit:
- https://msdl.microsoft.com/download/symbols/bootmgfw.efi/7144BCD31C0000/bootmgfw.efi
- https://msdl.microsoft.com/download/symbols/bootmgr.efi/98B063A61BC000/bootmgr.efi
- https://msdl.microsoft.com/download/symbols/hvloader.efi/559F396411D000/hvloader.Efi
Smolár explains that operator CVE-2022-21894 is what allows BlackLotus to bypass Secure Boot and establish perseverance after deactivating HVCI (to load unsigned kernel code) and BitLockerComment (to allow changing the boot string without initiating the recovery procedure on systems with the Trusted Platform Module (TPM) hardware component):
- Exploit of CVE-2022-21894 to allow bypassing Secure Boot and installing the bootkit. Arbitrary code can then be executed in the early stages of booting, where the platform still belongs to the firmware and the functions of UEFI boot services are still available. This allows attackers to do many things that they shouldn’t be able to do on a machine with UEFI Secure Boot enabled without having physical access to it, such as modifying boot-only services NVRAM variables. And that’s what attackers take advantage of to set up bootkit persistence in the next step.
- Setting persistence by writing its own MOK to the NVRAM variable MokList, Boot-services-only. By doing so, he can use a legitimate Microsoft-signed shim to load his self-signed UEFI boot kit (signed by the private key belonging to the key written in MokList) instead of exploiting the vulnerability every time he boots.
Note, proof of concept (PoC) exploit code for CVE-2022-21894 has been publicly available for over six months, since August 2022. However, the issue of security has been largely ignored.
Microsoft patching the vulnerability in June 2022 was not enough to close the security gap as the UEFI DBX (UEFI revocation list) has not yet been updated with untrusted keys and binary hashes used in boot systems that have Secure Boot enabled.
“As a result, attackers can bring their own copies of vulnerable binaries to their victims’ machines to exploit this vulnerability and bypass Secure Boot on up-to-date UEFI systems” – ESET
Last year, researchers revealed several UEFI vulnerabilities [1, 2] which could also be exploited to disable Secure Boot. However, some of them can still be exploited due to vendors no longer supporting the affected devices, incorrect patches, or no patches at all.
Smolár says these failures were to attract the attention of a threatening actor and lead to the creation of a high-performance UEFI bootkit.
UEFI Malware
UEFI bootkits are the opposite of common malware. These are rare findings seen in attacks attributed to advanced threat actors working on behalf of a nation state.
Although proof-of-concept bootkits have been around since 2013 (e.g. DreamBoot) and malicious EFI bootloaders that prevented the machine from booting were discovered in 2020, the list of full-featured bootkits used in actual attacks is incredibly short:
- FinSpy – part of the homonymous monitoring toolset (aka FinFisher, WingBird)
- ESPector – a patched Windows boot manager on the EFI (Extensible Firmware Interface) system partition
- CosmicStrand/Shadow Trojan Spy – a UEFI threat that lurked in the firmware images of ASUS and Gigabyte motherboards to deploy a kernel-level implant every time the compromised Windows machine boots
Records for the larger UEFI malware category, which also includes rootkits or firmware implants, aren’t much larger.
In 2018, ESET exhibited the LoJax UEFI Rootkit used by Russian hackers from the APT28 group (Sednit/Fancy Bear/Sofacy).
Two years later, Kaskpersky publishes a report on the MosaicRegressor rootkit that served Chinese hackers in data theft and espionage operations in 2019.
In early 2022, another UEFI firmware implant was leaked. moon bounce was attributed to the Chinese-speaking group APT41/Winnti.
However, BlackLotus is the first publicly leaked UEFI bootkit that bypasses Secure Boot and is associated with the cybercriminal world.
[ad_2]
Source link
