[ad_1]

Antivirus firm Bitdefender has released a decryptor for the MegaCortex ransomware family, allowing victims of the once notorious gang to restore their data for free.
The creation of the decryptor is the combined work of Bitdefender analysts and experts from Europol, the NoMoreRansom project, the Zürich public prosecutor’s office and the cantonal police.
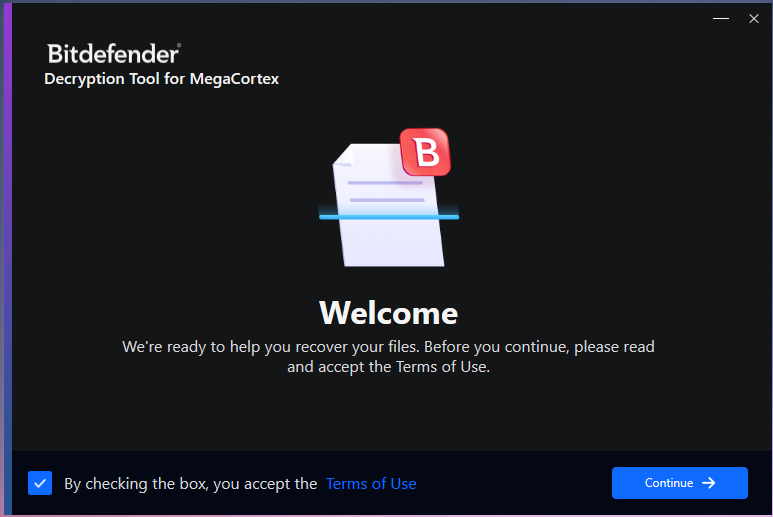
Using the decryptor is quite simple, as it is a standalone executable that does not require installation and offers to automatically locate encrypted files on the system.
Moreover, the decryptor can back up the encrypted files for security reasons in case something goes wrong in the decryption process that might corrupt the files beyond recovery.
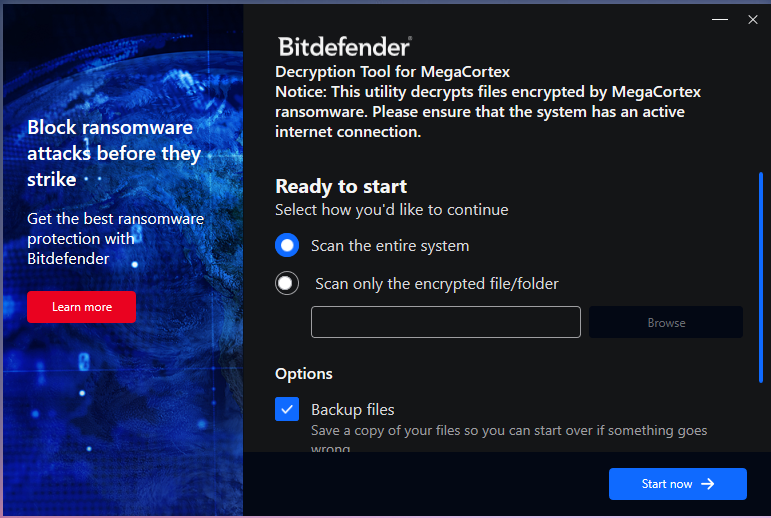
Moreover, for those who have already tried to decrypt their files with mixed success, the new decryptor offers an advanced setting to replace them with clean files.
You can download the tool from this page and read the User’s Guide for more details on using Bitdefender’s MegaCortex decryptor.
The rise and fall of MegaCortex
MegaCortex ransomware was first discovered by Sophos researchers in May 2019who observed him targeting corporate networks and found him with QBot, Emotet, and Cobalt Strike.
Captured samples in July 2019 revealed that MegaCortex operators were launching more targeted attacks, adjusting ransom demands based on the size of the victim, and using particularly threatening language.
In November 2019MegaCortex operators began engaging in double extortion tactics, threatening victims with the release of their data if they did not comply with their demands.
At the end of this month, the Dutch National Cybersecurity Center placed MegaCortex among the most active ransomware operations in cybercrime basement.
In December 2019, the The FBI Warned organizations on the MegaCortex threat, describing the intrusion methods used by the threat group and providing defense tips and mitigation recommendations.
Throughout 2020, MegaCortex activity decreased and there were not many victims affected by this particular strain.
In October 2021, Europol announced the arrest of 12 people responsible for 1,800 ransomware attacks in 71 countries, many of which deployed the MegaCortex and LockerGoga strains.
This arrest eventually led to the release of a free LockerGoga ransomware decryptor by BitDefender in September after authorities discovered private keys used in attacks.
“This analysis revealed numerous private keys from ransomware attacks. These keys allow damaged companies and institutions to restore data previously encrypted with the ‘LockerGoga’ or ‘MegaCortex’ malware,” a coordinated official said. announcement by the Zurich public prosecutor’s office.
Although BitDefender did not indicate how they obtained the private keys for today’s MegaCortex decryptor, it was probably created with master keys found by authorities in Zurich.
[ad_2]
Source link
