[ad_1]

New Android malware distributed as an advertising SDK has been discovered in multiple apps, many of which were previously on Google Play and collectively downloaded over 400 million times.
Dr. Web security researchers discovered the spyware module and tracked it as “SpinOk”, warning that it can steal private data stored on users’ devices and send it to a remote server .
The antivirus company says SpinkOk exhibits seemingly legitimate behavior, using mini-games that lead to “daily rewards” to pique user interest.
“On the surface, the SpinOk module is designed to keep users interested in apps using mini-games, a task system, and pretend prizes and reward drawings,” explains Doctor Web’s Report.
In the background, however, the Trojan SDK checks the Android device’s sensor data (gyroscope, magnetometer) to confirm that it is not operating in a sandboxed environment, which is commonly used by researchers during analysis of potentially malicious Android applications.
The app then connects to a remote server to download a list of open URLs used to display expected minigames.
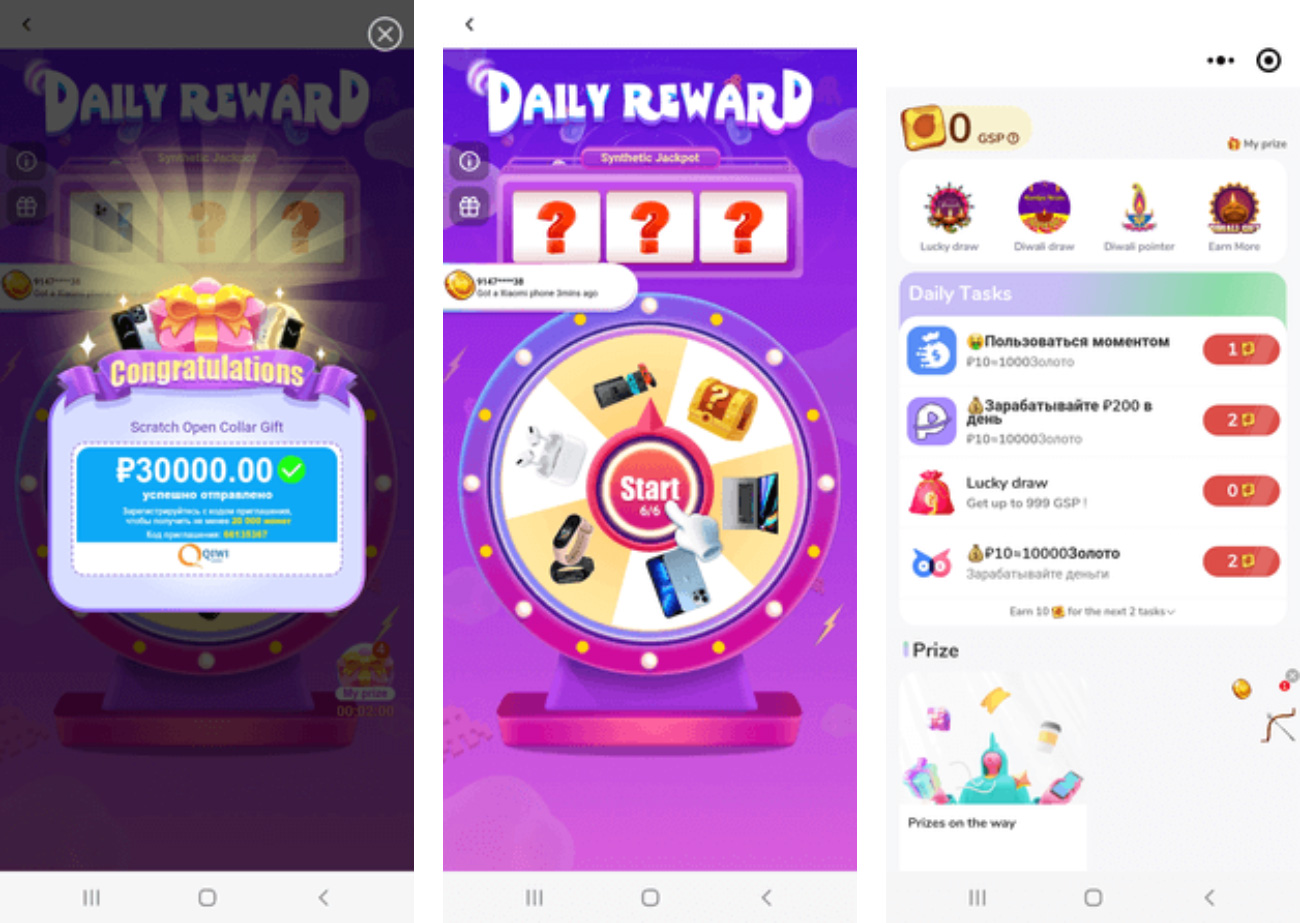
Source: Dr Web
While minigames are displayed to app users as intended, Dr. Web says that behind the scenes, the SDK is capable of additional malicious functionality, including listing files in directories, searching for particular files , downloading files from the device or copying. and replace the contents of the clipboard.
The file exfiltration feature is of particular concern as it could expose private images, videos and documents.
Additionally, the clipboard modification feature code allows SDK operators to steal account passwords and credit card data, or divert cryptocurrency payments to their own crypto wallet addresses. .
Dr. Web claims that this SDK was found in 101 apps that were downloaded for a cumulative total of 421,290,300 times from Google Play, with the most downloaded listed below:
- Noizz: video editor with music (100,000,000 downloads)
- Zapya – File Transfer, Sharing (100,000,000 downloads; Dr. Web says the Trojan module was present in version 6.3.3 to version 6.4 and is no longer present in the current version 6.4.1)
- VFly: video editor and video creator (50,000,000 downloads)
- MVBit – MV Video Status Maker (50,000,000 downloads)
- Biugo – videographer and video editor (50,000,000 downloads)
- Crazy Drop (10,000,000 downloads)
- Cashzine – Earn cash rewards (10,000,000 downloads)
- Fizzo Novel – Offline Reading (10,000,000 downloads)
- CashEM: get rewards (5,000,000 downloads)
- Tick: watch to win (5,000,000 downloads)
All but one of the above apps have been removed from Google Play, indicating that Google has received reports of the malicious SDK and removed the offending apps until the developers submit a clean version.
A full list of apps that are supposed to use the SDK can be found at Dr Web’s website.
It is not known whether the publishers of the trojanized apps were tricked by the SDK’s distributor or knowingly included it in their code, but such infections are usually the result of a third-party supply chain attack.
If you are using any of the apps listed above, you should update to the latest version available through Google Play, which should be clean.
If the application is not available on the official Android application store, it is recommended to uninstall it immediately and scan your device with a mobile antivirus tool to ensure that all remnants of spyware are removed .
BleepingComputer has contacted Google for a statement on this massive infection basis, but no comment was available at the time of publication.
[ad_2]
Source link
