[ad_1]

A new mobile malware campaign since March 2023 is pushing the Android banking trojan “Anatsa” to online banking customers in the US, UK, Germany, Austria and Switzerland.
According to security researchers from Threat Fabricwho tracked the malicious activity, the attackers distribute their malware through the Play Store, Android’s official app store, and already have over 30,000 installs through this method alone.
ThreatFabric discovered a previous Anatsa campaign on Google Play in November 2021, when the Trojan was installed over 300,000 times by impersonating PDF scanners, QR code scanners, Adobe Illustrator apps, and fitness tracking apps.
New Anatsa campaign
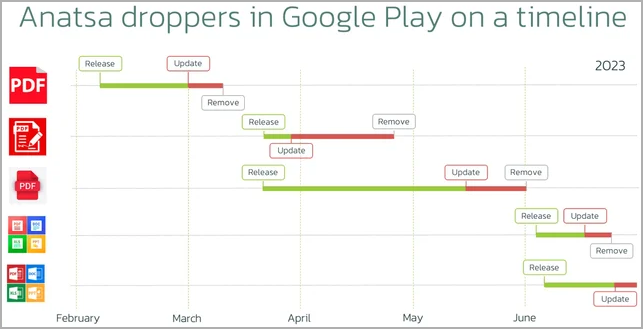
In March 2023, after a six-month hiatus in malware distribution, threat actors launched a new malicious advertising campaign that leads potential victims to download Anatsa dropper apps from Google Play.
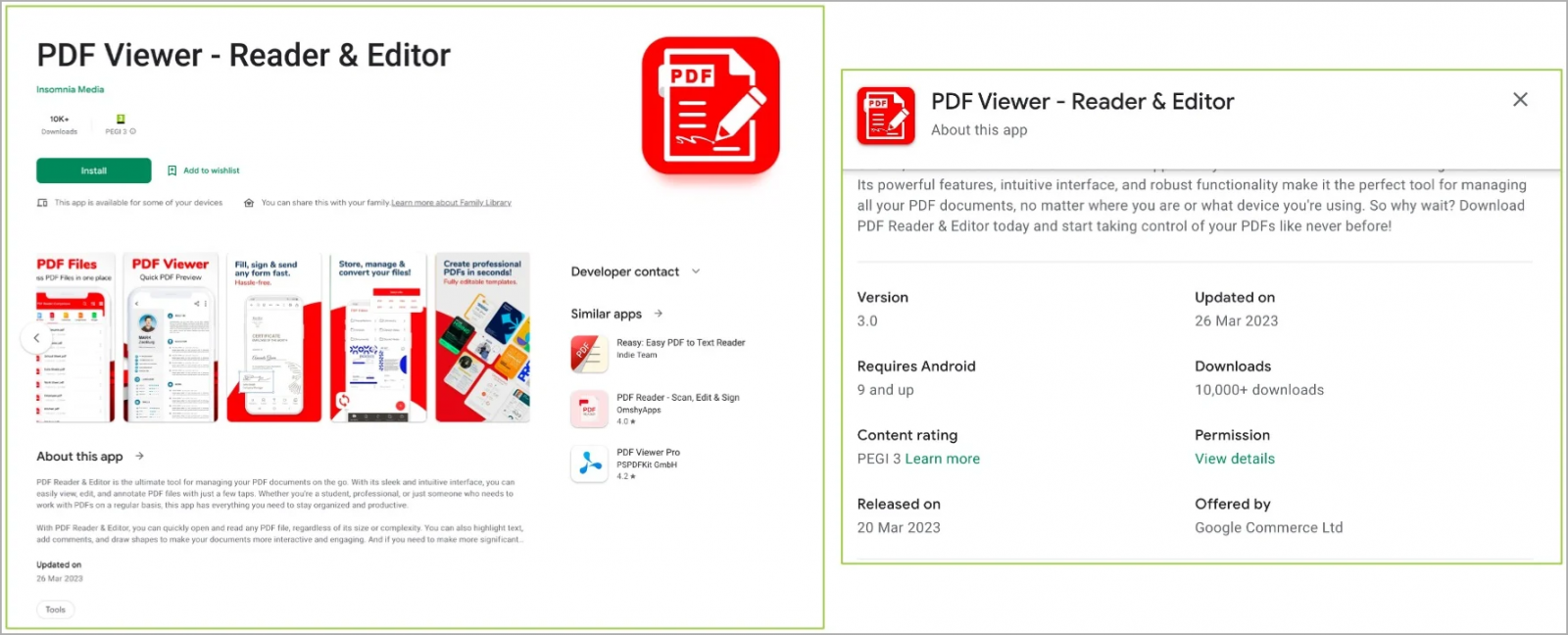
Malicious apps continue to fall into the office/productivity category, masquerading as PDF viewing and editing apps and office suites.
Each time ThreatFabric reported the malicious app to Google and it was removed from the store, the attackers quickly returned by uploading a new dropper in a new guise.
In all five cases of identified malware droppers, the apps were submitted to Google Play in a clean form and were later updated with malicious code, likely to evade Google’s rigorous code review process during of the first submission.
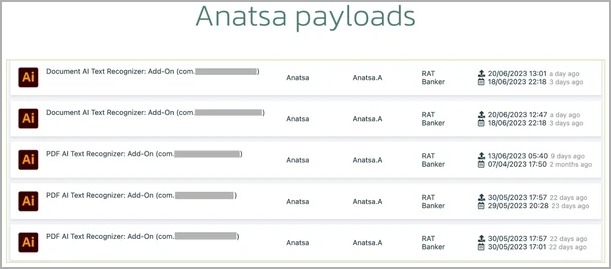
Once installed on the victim’s device, the dropper applications request an external resource hosted on GitHub, from which they download Anatsa payloads disguised as text recognition add-ons for Adobe Illustrator.
Anatsa collects financial information such as bank account credentials, credit card details, payment information, etc., by overlaying phishing pages in the foreground when the user tries to launch their banking app legitimate and also via keylogging.
In its current version, the Anatsa Trojan supports the targeting of almost 600 financial applications from banking institutions around the world.
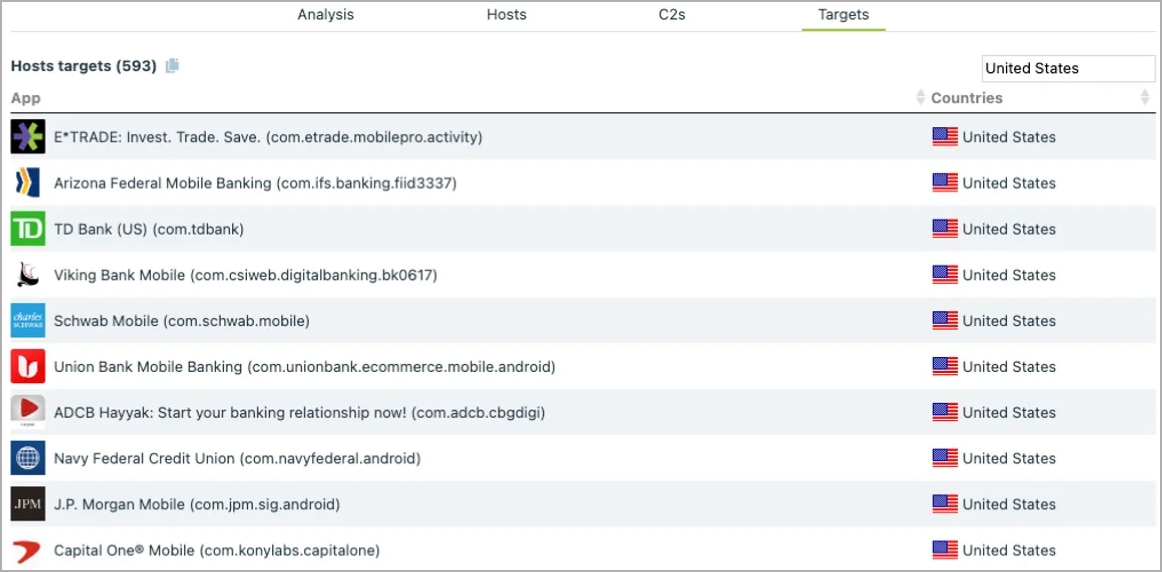
Anatsa uses the stolen information to perform fraud on the device by launching the banking app and performing transactions on behalf of the victim, automating the money theft process for its operators.
“Because the transactions are initiated from the same device that the targeted bank customers regularly use, it has been reported that it is very difficult for bank anti-fraud systems to detect it,” says ThreatFabric.
The stolen amounts are converted into cryptocurrency and transmitted through a large network of money mules in the targeted countries, who will keep part of the stolen funds as revenue share and send the rest to the attackers.
Protect Android
As malware campaigns, such as Anatsa, expand their targeting to other countries, users need to be extremely vigilant about the apps they install on Android devices.
Users should avoid installing apps from dubious publishers, even if they are on a well-controlled store like Google Play. Always check reviews and see if a reporting pattern indicates malicious behavior.
Also, if possible, avoid apps with few installs and reviews and instead install well-known and frequently cited apps on websites.
As many apps on Google Play have the same name as malicious apps, it is recommended to see the appendix of the ThreatFabric report for the list of package names and signatures pushing Anatsa and immediately remove them from your Android device if installed.
BleepingComputer asked Google to explain how Anatsa operators can submit malicious updates to their dropper apps on the Play Store and quickly replace reported droppers, but no comment was available per post. .
[ad_2]
Source link
