[ad_1]

The consumer Microsoft signing key stolen by Chinese hackers Storm-0558 gave them access well beyond the Exchange Online and Outlook.com accounts that Redmond believed were compromised, according to Wiz security researchers.
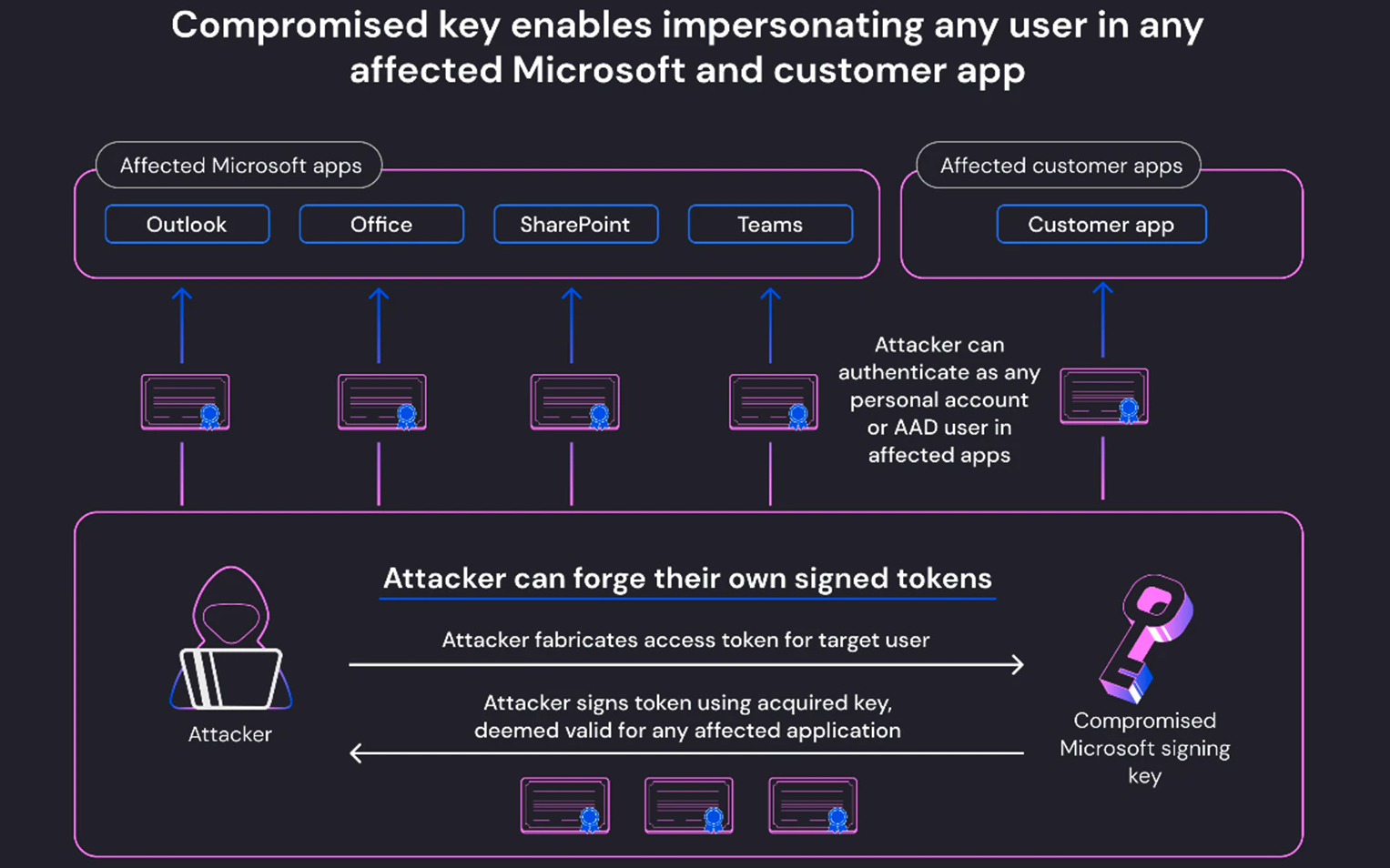
Redmond revealed on July 12 that attackers hacked the Exchange Online and Azure Active Directory (AD) accounts of approximately two dozen organizations. This was achieved by exploiting a now fixed zero-day validation issue in the GetAccessTokenForResource API, allowing them to forge signed access tokens and impersonate accounts within the targeted organizations.
Entities involved included government agencies in the United States and parts of Western Europe, with United States Departments of State and Commerce among them.
On Friday, security researcher Wiz Shir Tamari said that the impact extended to all Azure AD applications running on Microsoft’s OpenID v2.0. This was due to the ability of the stolen key to sign any OpenID v2.0 access token for personal accounts (eg Xbox, Skype) and multi-tenant AAD applications.
Microsoft clarified after this article was published that it only affects those who accept personal accounts and have the validation error.
While Microsoft said only Exchange Online and Outlook were affected, Wiz says threat actors could use the compromised Microsoft Customer Signing Key to impersonate any account within any cloud-based Microsoft customer or application.
“This includes managed Microsoft apps, such as Outlook, SharePoint, OneDrive and Teams, as well as customer apps that support Microsoft account authentication, including those that allow ‘Sign in with Microsoft’ functionality,” Tamari said.
“Everything in Microsoft uses Azure Active Directory authentication tokens for access,” Wiz CTO and co-founder Ami Luttwak also told BleepingComputer.
“An attacker with an AAD signing key is the most powerful attacker you can imagine, as they can access almost any application – just like any user. This is the ultimate cyber intelligence ‘shape-transformer’ superpower.”
In response to the security breach, Microsoft revoked all valid MSA signing keys to ensure threat actors do not have access to other compromised keys.
This measure also thwarted any attempt to generate new access tokens. Additionally, Redmond has moved the newly generated access tokens to the company’s Enterprise Systems Keystore.
After invalidating the stolen signing key, Microsoft found no further evidence to suggest additional unauthorized access to its customers’ accounts using the same authentication token forgery technique.
Additionally, Microsoft reported observing a change in Storm-0558 tactics, showing that threat actors no longer had access to any signing keys.
Finally, the company revealed last Friday that it still don’t know how Chinese hackers stole Microsoft’s consumer signing key. However, after pressure from CISA, they agreed to extend access to cloud log data for free to help defenders detect similar breach attempts in the future.
Previously, these logging features were only available to Microsoft customers who paid for a Purview Audit (Premium) logging license. As a result, Microsoft has been heavily criticized for preventing organizations from early detection of Storm-0558 attacks.
“At this point, it is difficult to determine the full scope of the incident as there were millions of potentially vulnerable applications, both Microsoft applications and client applications, and the majority of them do not have sufficient logs to determine whether or not they were compromised,” Tamari concluded today.
Update 7/22/23: Article updated with clarifications from Microsoft.
[ad_2]
Source link
