[ad_1]

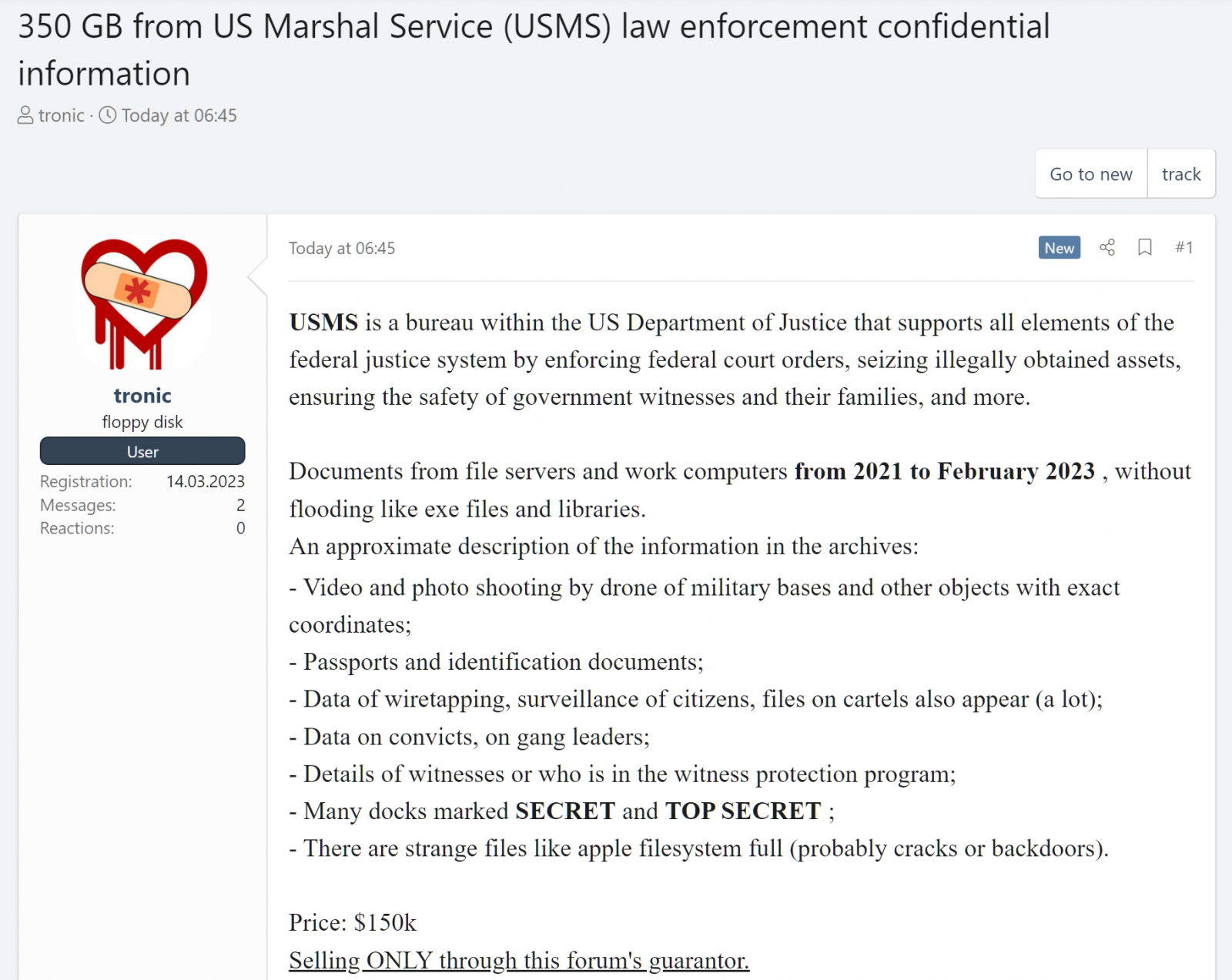
A malicious actor is selling what he claims is hundreds of gigabytes of data stolen from US Marshals Service (USMS) servers on a Russian-language hacking forum.
The USMS is an office of the Department of Justice that provides support to the federal justice system by enforcing federal court orders, providing security for government witnesses and their families, seizing illegally obtained property, and more.
The announcement, titled “350GB of confidential law enforcement information from the US Marshal Service (USMS)”, was posted earlier today using a registered account yesterday afternoon.
According to the vendor, the database is sold for $150,000 and contains “documents from file servers and work computers from 2021 through February 2023, unflooded like exe files and libraries,” according to the vendor.
The information includes aerial footage and photos of military bases and other high-security areas, copies of passports and identity documents, and details of wiretapping and citizen surveillance.
The files also contain information on convicts, gang leaders and cartels. The threat author also claims that some files are marked as SECRET or TOP SECRET.
The threat actor also claims that the database contains details of witnesses under the witness protection program.
A USMS spokesperson was unavailable for comment when contacted by BleepingComputer today for a statement regarding allegations that data stolen in last month’s incident is now for sale.
USMS investigates ransomware attack
It comes after the USMS confirmed last month that it was investigating a “data exfiltration event” after a ransomware attack on February 17 this impacted what he described as “a stand-alone USMS system”.
According to USMS spokesperson Drew Wade, the data stolen in this incident, labeled a “major incident,” includes the personally identifiable information of USMS employees.
“The affected system contains sensitive law enforcement information, including court process returns, administrative information, and personally identifiable information about USMS investigation subjects, third parties, and certain USMS employees. USMS,” Wade said.
However, sources close to the incident told NBC News that the attackers did not have access to the USMS Witness Security Files Information System database (also known as WITSEC or witness protection program).
The USMS disclosed another data breach in May 2020 after exposed details of more than 387,000 former and current detainees in a December 2019 incident, including their names, dates of birth, home addresses and social security numbers.
The US Federal Bureau of Investigation (FBI) has also disclosed a cybersecurity incident two weeks ago, described as an “isolated incident” now contained.
[ad_2]
Source link
