[ad_1]

Cyber espionage hacking group Sharp Panda is targeting high-profile government entities in Vietnam, Thailand and Indonesia with a new version of the “Soul” malware framework.
The particular malware has already been seen in spy campaigns targeting critical organizations in Southeast Asia, attributed to various Chinese APTs.
Checkpoint identified a new campaign using the malware that began in late 2022 and continues through 2023, using spear phishing attacks as an initial compromise.
Using the RoyalRoad RTF kit, C2 server addresses and the hacker’s working hours allowed Check Point to attribute the latest spy operation to state-backed Chinese hackers. TTPs and tools are consistent with activities previously observed by Sharp Panda.
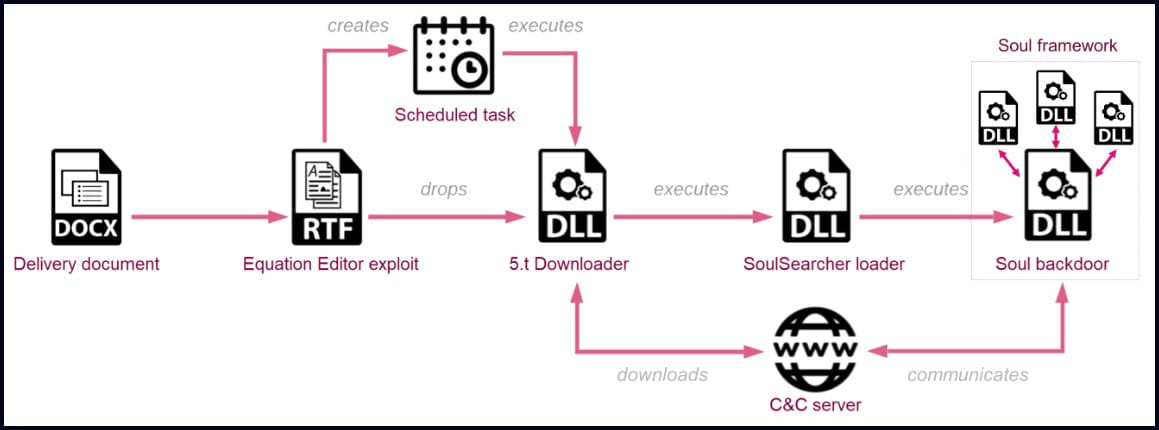
Chain of infection
The new Sharp Panda campaign uses spear phishing emails with malicious DOCX attachments that deploy the RoyalRoad RTF kit in an attempt to exploit old vulnerabilities to drop malware onto the host.
In this case, the exploit creates a scheduled task, then drops and runs a malware downloader DLL, which in turn fetches and runs a second DLL from the C2 server, the SoulSearcher loader.
This second DLL creates a registry key with a value that contains the final compressed payload, then decrypts and loads the Soul modular backdoor into memory, helping it evade detection from antivirus tools running on the hacked system.
Soul details
While running, the core Soul malware module establishes a connection with the C2 and waits for additional modules that will extend its functionality.
The new version analyzed by Check Point offers a “radio silence” mode that allows threat actors to specify specific times of the week when the backdoor should not communicate with the command and control server, likely to escape to detection during the victim’s working hours.
“This is an advanced OpSec feature that allows actors to integrate their communication flow into general traffic and reduce the risk of network communication being detected.” explained Check Point.
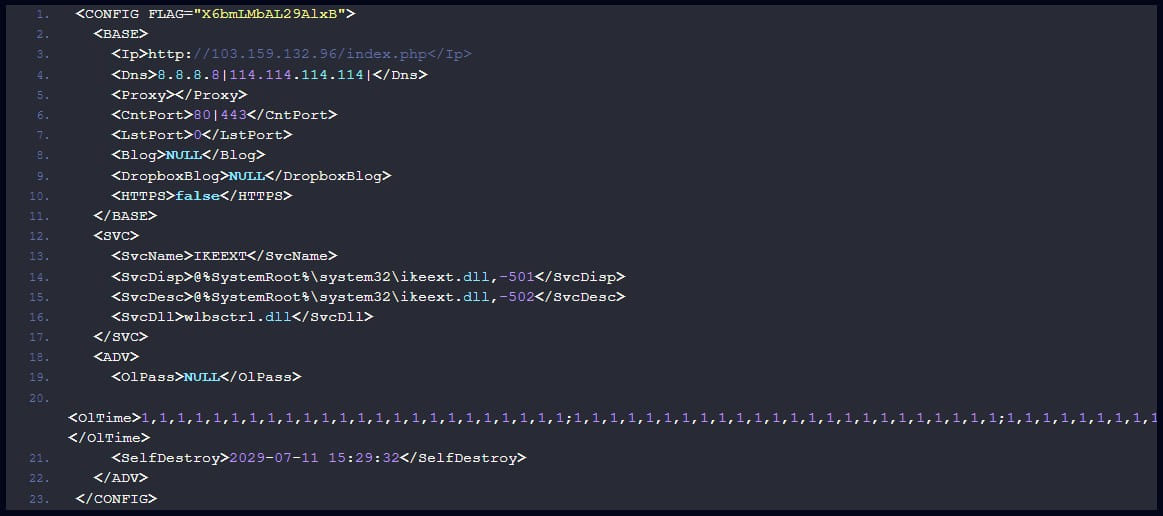
Additionally, the new variant implements a custom C2 communication protocol that uses various HTTP request methods including GET, POST, and DELETE.
Support for multiple HTTP methods gives the malware flexibility, as GET is used to retrieve data, POST to submit data.
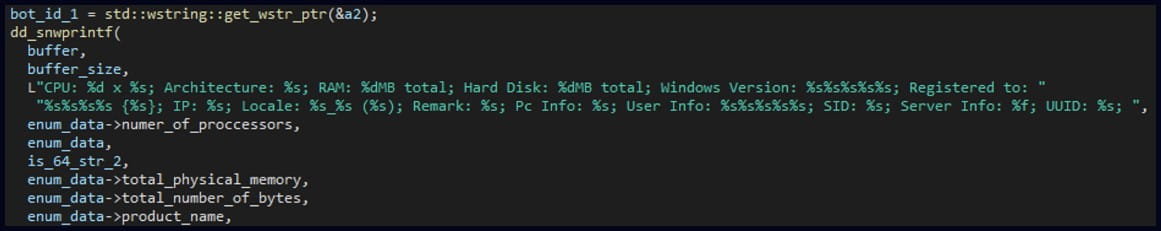
Soul’s communication with the C2 begins with registering and sending the victim’s fingerprint data (hardware details, operating system type, time zone, IP address), after which it enters a loop of infinite contact C2.
The commands it can receive during these communications relate to the loading of additional modules, the collection and retransmission of enumeration data, the restarting of the C2 communication or the exit of its process.
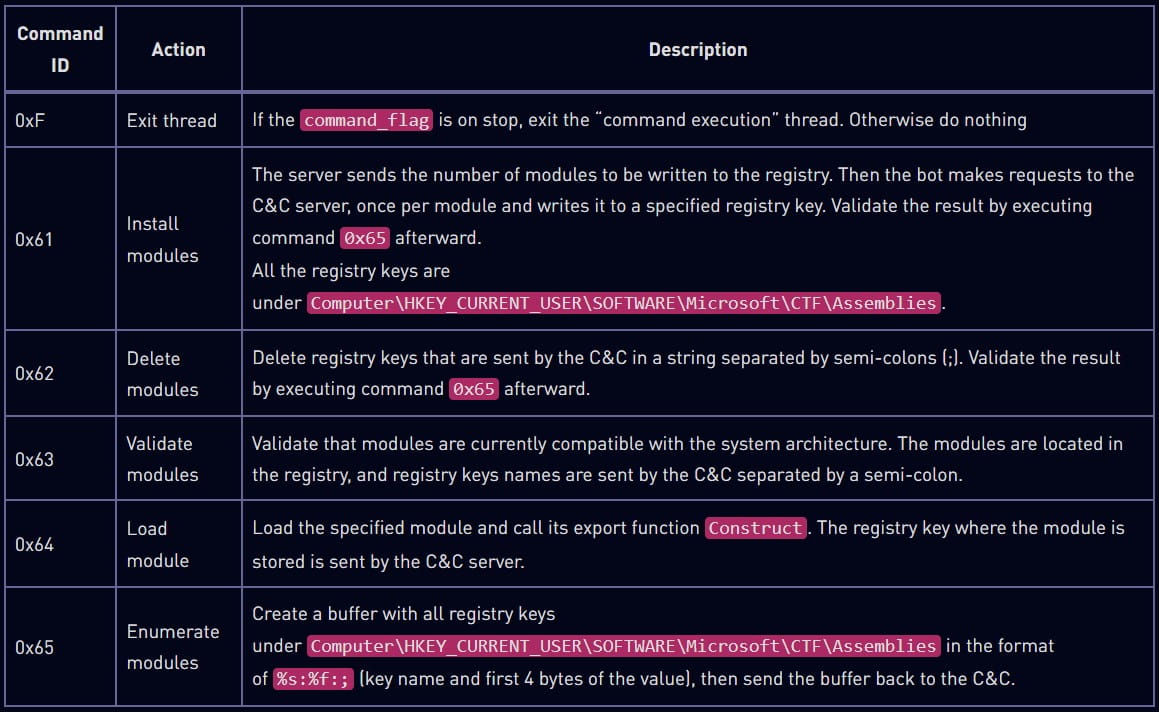
Check Point has not sampled additional modules that could perform more specialized functions such as file actions, data exfiltration, keylogging, screen capturing, etc.
The Soul framework was first seen in the wild in 2017 and then tracked throughout 2019 in Chinese spy campaigns by threat actors with no obvious connection to Sharp Panda.
Despite the overlaps in the use of the tool, recent findings from Check Point show that Soul is still under development and deployment.
[ad_2]
Source link
