[ad_1]

Cybersecurity researchers have discovered a fundamental security flaw in the design of the IEEE 802.11 WiFi protocol standard, allowing attackers to trick access points into leaking network frames as plaintext.
WiFi frames are data containers consisting of a header, data payload, and trailer, which include information such as source and destination MAC address, control data, and management.
These frames are ordered into queues and transmitted in a controlled manner to avoid collisions and maximize data exchange performance by monitoring the busy/idle states of the receiving points.
Researchers have found that enqueued/buffered frames are not sufficiently protected against adversaries, who can manipulate data transmission, client spoofing, frame redirection, and capture.
“Our attacks have widespread impact because they affect various devices and operating systems (Linux, FreeBSD, iOS, and Android) and because they can be used to hijack TCP connections or intercept client and web traffic,” reads- on in the technical paper published yesterday by Domien Schepers and Aanjhan Ranganathan of Northeastern University, and Mathy Vanhoef of imec-DistriNet, KU Leuven.
Energy saving fault
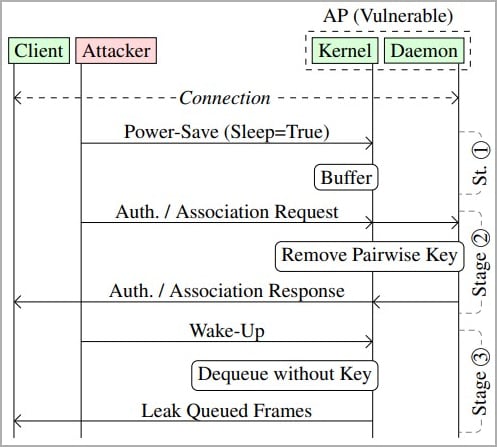
The IEEE 802.11 standard includes power-saving mechanisms that allow WiFi devices to save power by buffering or queuing frames destined for sleeping devices.
When a client station (receiver device) enters sleep mode, it sends a frame to the access point with a header containing the power save bit, so all frames destined for it are dropped. in queue.
The standard, however, does not provide explicit guidance on the security management of these queued frames and does not define limits such as how long frames can remain in this state.
After the client station wakes up, the access point removes the buffered frames, applies encryption, and forwards them to the destination.
An attacker can spoof the MAC address of a device on the network and send power saving frames to access points, forcing them to queue frames destined for the target. Next, the attacker transmits a wake-up frame to recover the frame stack.
Transmitted frames are usually encrypted using the group-addressed encryption key, shared between all devices on the WiFi network, or a pairwise encryption key, unique to each device and used to encrypt frames exchanged between two devices.
However, the attacker can modify the security context of the frames by sending authentication and association frames to the access point, thereby forcing it to transmit the frames as plain text or encrypt them with a key. provided by the attacker.
This attack is possible using custom tools created by the researchers called macstealerwhich can test Wi-Fi networks for client isolation bypasses and intercept traffic destined for other clients at the MAC layer.
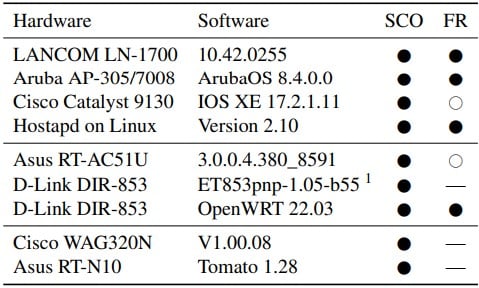
Researchers report that network device models from Lancom, Aruba, Cisco, Asus, and D-Link are known to be affected by these attacks, with the full list below.
The researchers warn that these attacks could be used to inject malicious content, such as JavaScript, into TCP packets.
“An adversary can use their own Internet-facing server to inject data into this TCP connection by injecting off-path TCP packets with a spoofed sender IP address,” the researchers warn.
“This can, for example, be abused to send malicious JavaScript code to the victim over plain HTTP connections in an attempt to exploit vulnerabilities in the client’s browser.”
Although this attack could also be used to spy on traffic, since most web traffic is encrypted using TLS, the impact would be limited.
Technical details and research are available in Document USENIX Safety 2023which will be presented at the next BlackHat Asia Conference May 12, 2023.
Cisco recognizes a flaw
The first vendor to acknowledge the impact of the WiFi protocol flaw is Cisco, admitting that the attacks described in the document could succeed against Cisco Wireless Access Point products and Cisco Meraki products with wireless capabilities.
However, Cisco believes that the recovered frames are unlikely to compromise the overall security of a properly secured network.
“This attack is considered an opportunistic attack, and the information obtained by the attacker would be of minimal value in a securely configured network.” – Cisco.
Nevertheless, the company recommends applying mitigation measures such as the use of policy enforcement mechanisms through a system such as Cisco Identity Services Engine (ISE), which can restrict network access by implementing Cisco TrustSec or Software Defined Access (SDA) technologies.
“Cisco also recommends implementing transport layer security to encrypt data in transit whenever possible, as this would render acquired data unusable by the attacker,” reads the Cisco Security Advisory.
Currently, there are no known cases of malicious use of the flaw discovered by the researchers.
[ad_2]
Source link
