[ad_1]

Microsoft says cryptocurrency investment firms have been targeted by a group of threats it tracks as DEV-0139 through Telegram groups used to communicate with corporate VIP customers.
“Microsoft recently investigated an attack where the threat actor, tracked as DEV-0139, took advantage of Telegram chat groups to target cryptocurrency investment firms,” the team said. Company Security Threat Intelligence. revealed.
“DEV-0139 joined Telegram groups used to facilitate communication between VIP customers and cryptocurrency exchanges and identified their target among members.”
On October 19, attackers with broad knowledge of the crypto investment industry invited at least one target (posing as representatives of other crypto asset management companies) to another Telegram group, where they asked for feedback on the fee structure of cryptocurrency exchange platforms.
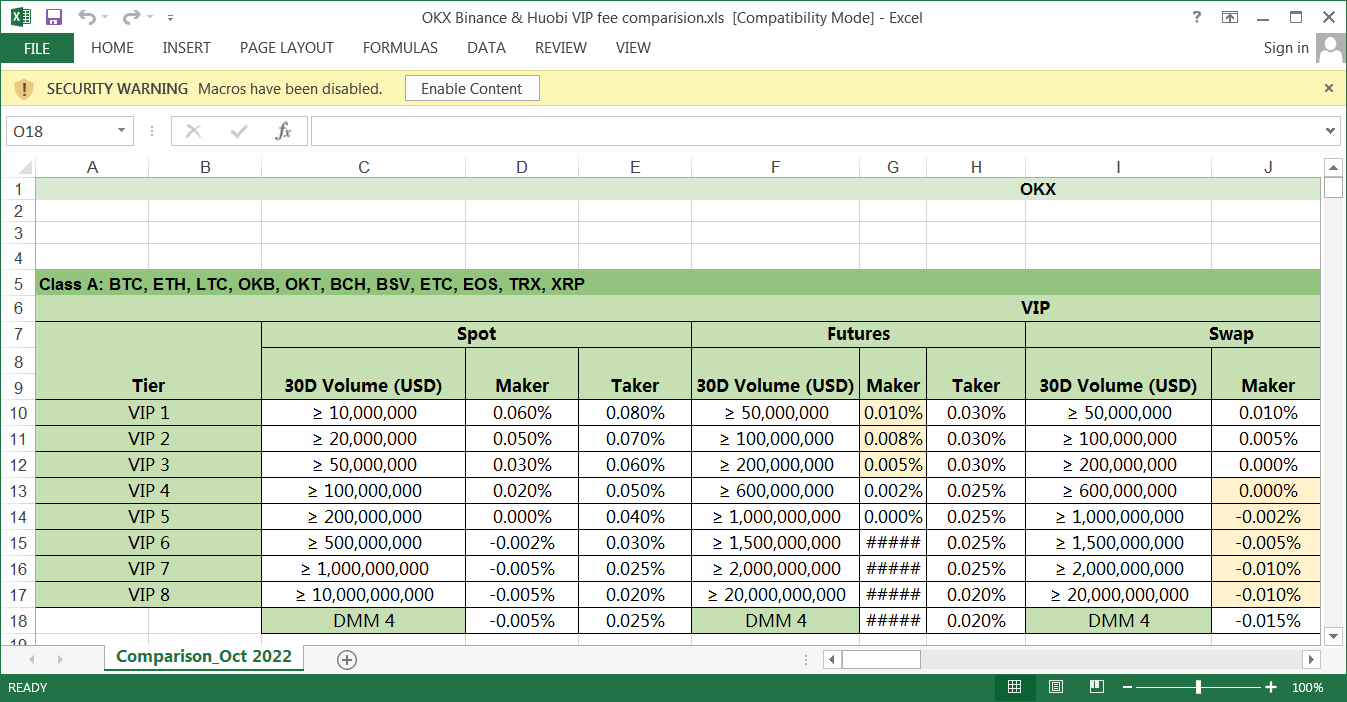
After gaining the trust of their targets, the threat actors sent them malicious Excel spreadsheets named “OKX Binance & Huobi VIP fee comparision.xls” with a data comparison (presumably accurate to increase credibility) between the VIP fee structures of crypto exchange companies.
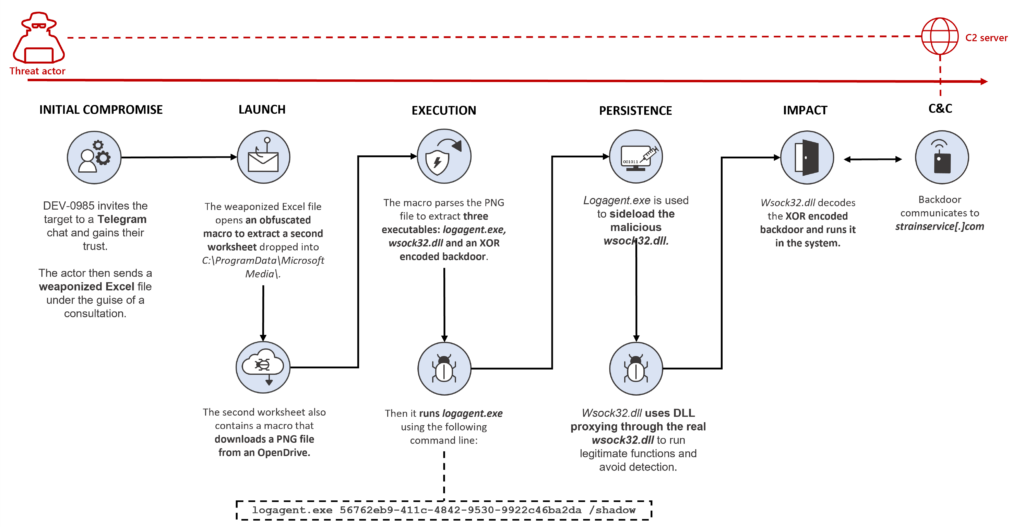
After the victim opens the document and enables macros, a second spreadsheet embedded in the file downloads and parses a PNG file to extract a malicious DLL, an XOR-encoded backdoor, and a legitimate Windows executable later used to load the DLLs.
This DLL will decrypt and load the backdoor, giving attackers remote access to the victim’s compromised system.
“The main sheet of the Excel file is protected by the password dragon to encourage the target to enable macros,” Microsoft explained.
“The sheet is then unprotected after installing and running the other Excel file stored in Base64. This is likely used to trick the user into enabling macros and not arousing suspicion.”
DEV-0139 also delivered a second payload as part of this campaign, an MSI package for a CryptoDashboardV2 application, suggesting that they are also behind other attacks using the same technique to push custom payloads.
While Microsoft did not attribute this attack to any specific group and instead chose to link it to the DEV-0139 threat activity cluster, threat intelligence firm Volexity also released its own findings on this attack at over the weekend, linking it to the North. Korean threat group Lazarus.
According to Volexity, North Korean hackers used the malicious crypto exchange fee comparison spreadsheet to remove AppleJeus malware that Lazarus previously used in cryptocurrency hijacking and digital asset theft operations .
Volexity also observed that Lazarus was using a website clone for automated cryptocurrency trading platform HaasOnline to distribute a trojanized BloxHolder application that would instead deploy AppleJeus malware embedded in the QTBitcoinTrader application.
Microsoft says it notified customers who were compromised or targeted by these attacks and shared the information needed to secure their accounts.
The Lazarus Group is a hacking group operating out of North Korea that has been active for over a decade, since at least 2009.
Its operatives are known for their attacks on high-profile targets around the world, including banks, media and government agencies.
The group is believed to be responsible for high-profile cyberattacks, including the Sony Pictures Hack 2014 and the WannaCry ransomware attack of 2017.
[ad_2]
Source link
